EXPERIENCE
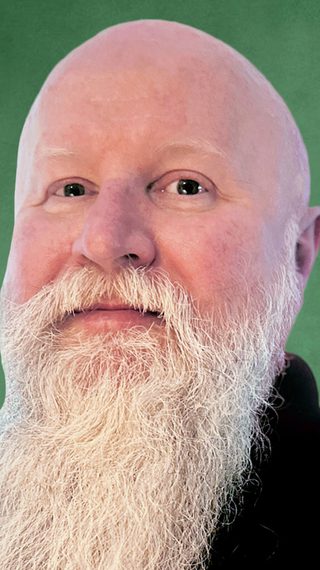
Lee Quinton has over 22 years of Network and Information Security experience. He began as a backbone engineer deploying GSRs and maintaining corporate firewalls but has worked predominantly as an InfoSec consultant since 2005. Lee has conducted compliance security assessments across a wide variety of verticals, against multiple industry frameworks, specializing in PCI, NIST, and ISO. Additionally, he’s been involved in many vulnerability assessments, penetration testing, and DFIR engagements over the years.
EDUCATION & CERTIFICATIONS
- Certified Information Systems Security Professional (CISSP)
- Certified Information Systems Auditor (CISA)
- Certified Data Privacy Solutions Engineer (CDPSE)
- Cybersecurity Maturity Model Certification Registered Practitioner (CMMC-RP)
- Payment Card Industry Qualified Security Assessor (QSA)
PROFESSIONAL AFFILIATIONS
- Northern England Information Systems Audit and Control Association (ISACA) Chapter
- International Information Systems Security Certification Consortium (ISC2)
PASSION FOR SECURITY
Lee has thoroughly enjoyed acting as a subject matter expert for a number of organizations over the years and has real passion for acting as a trusted advisor. Information Security is a continuous journey that is constantly evolving, and this has provided him with the opportunity to keep learning and growing as an InfoSec practitioner.
Featured Blogs And Resources
Discover the blogs, analysis, webinars, and podcasts by this team member.
Empower your business through better security design.
Talk directly with our experienced advisory consultants to learn how we can help.










