EXPERIENCE
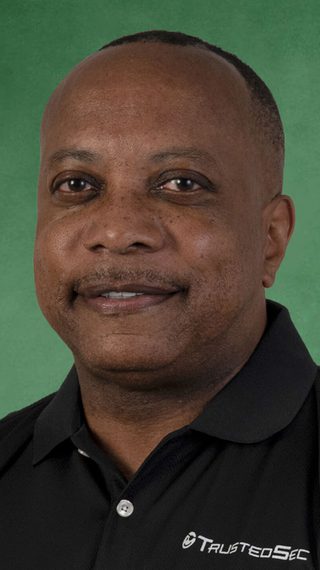
Jonathan White started his IT career in the United States Marine Corps as a Computer Programmer. After the Marine Corps, he started a job as a Computer Operator and advanced to serve as Manager of the company’s 24 X 7 data center. This is when he realized that providing solutions to issues and customer interaction was his passion. The next step in his career was as a Network Engineering Consultant for one of the national credit bureaus. In this role, he was responsible for the IP network for as many as 14 local offices in the Southern Region.
EDUCATION & CERTIFICATIONS
- Bachelor of Science in Business and Information Systems
- Certified Information Security Manager (CISM)
- Certified Information Systems Auditor (CISA)
- System Security Certified Practitioner (SSCP)
- Qualified Security Assessor (QSA)
- ISO 27001 Lead Auditor
PROFESSIONAL AFFILIATIONS
- Information Systems Audit and Control Association (ISACA)
PASSION FOR SECURITY
During his tenure at the national credit bureau, he was exposed to various regulatory compliance frameworks, developing an appreciation for the need to protect customers’ personal information. He secured a position with an Application Service Provider company as an IT Security Compliance Auditor responsible for monitoring their control environment and handling areas of both logical and physical security. He served in this capacity for over six years becoming familiar with several compliance frameworks, including SSAE18 SOC 1 and SOC2, ISO 27001, NIST, PCI DSS, and GLBA.
Featured Blogs And Resources
Discover the blogs, analysis, webinars, and podcasts by this team member.
Empower your business through better security design.
Talk directly with our experienced advisory consultants to learn how we can help.










