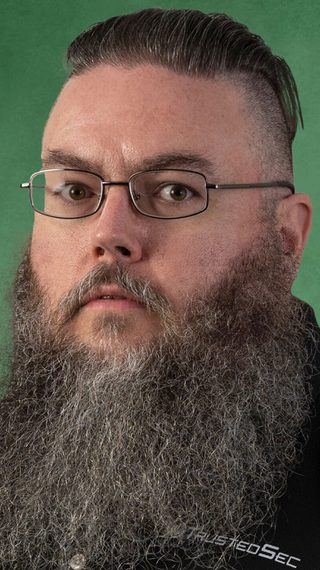
EXPERIENCE
Adam Compton has been a programmer, researcher, instructor, professional pen tester, father, husband, and farmer. Adam has nearly two decades of experience in programming, network security, incident response, security assessment, and penetration testing. Throughout Adam’s career, he has worked for both federal and international government agencies as well as the private sector.
EDUCATION & CERTIFICATIONS
- B.S. Computer Science – University of Kentucky
- B.S. Mathematics – University of Kentucky
INDUSTRY CONTRIBUTIONS
Adam has developed and contributed to several open source projects. Adam has also presented at a variety of conferences, from local BSides to BlackHat Europe.
PASSION FOR SECURITY
Adam’s passion for security originated with programming and has progressed through nearly the entire info gambit.
Featured Blogs And Resources
Discover the blogs, analysis, webinars, and podcasts by this team member.
Empower your business through better security design.
Talk directly with our experienced advisory consultants to learn how we can help.