October 27, 2017
TrevorC2 - Legitimate Covert C2 over Browser Emulation
Written by
TrustedSec
Penetration Testing
Security Testing & Analysis

TrustedSec is proud to announce the release of the TrevorC2 HTTP(s) command and control (C2) open source framework. TrevorC2 is a client/server model for masking command and control through a normally browsable website. Detection becomes much harder as time intervals are different and does not use POST requests for data exfiltration.
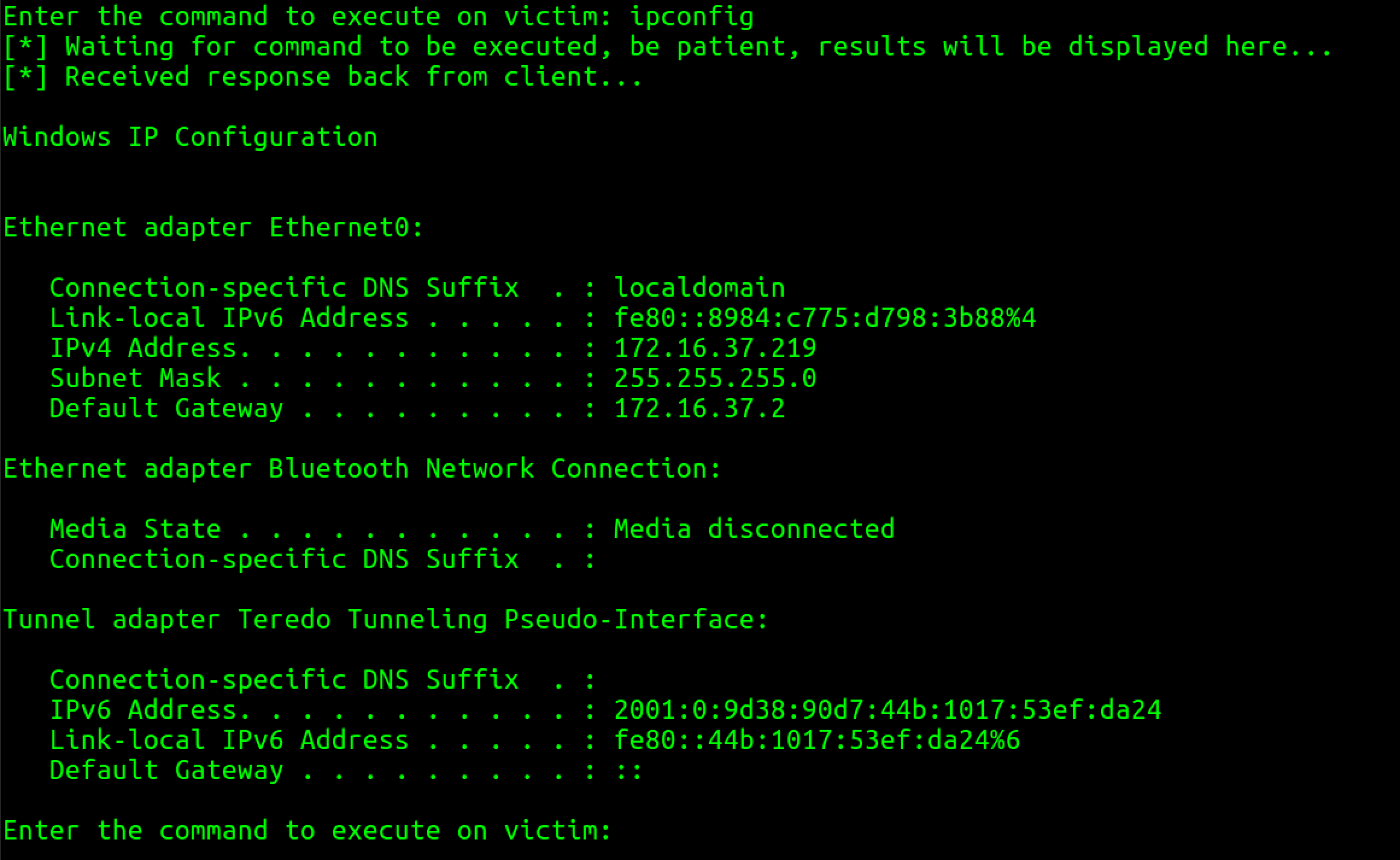
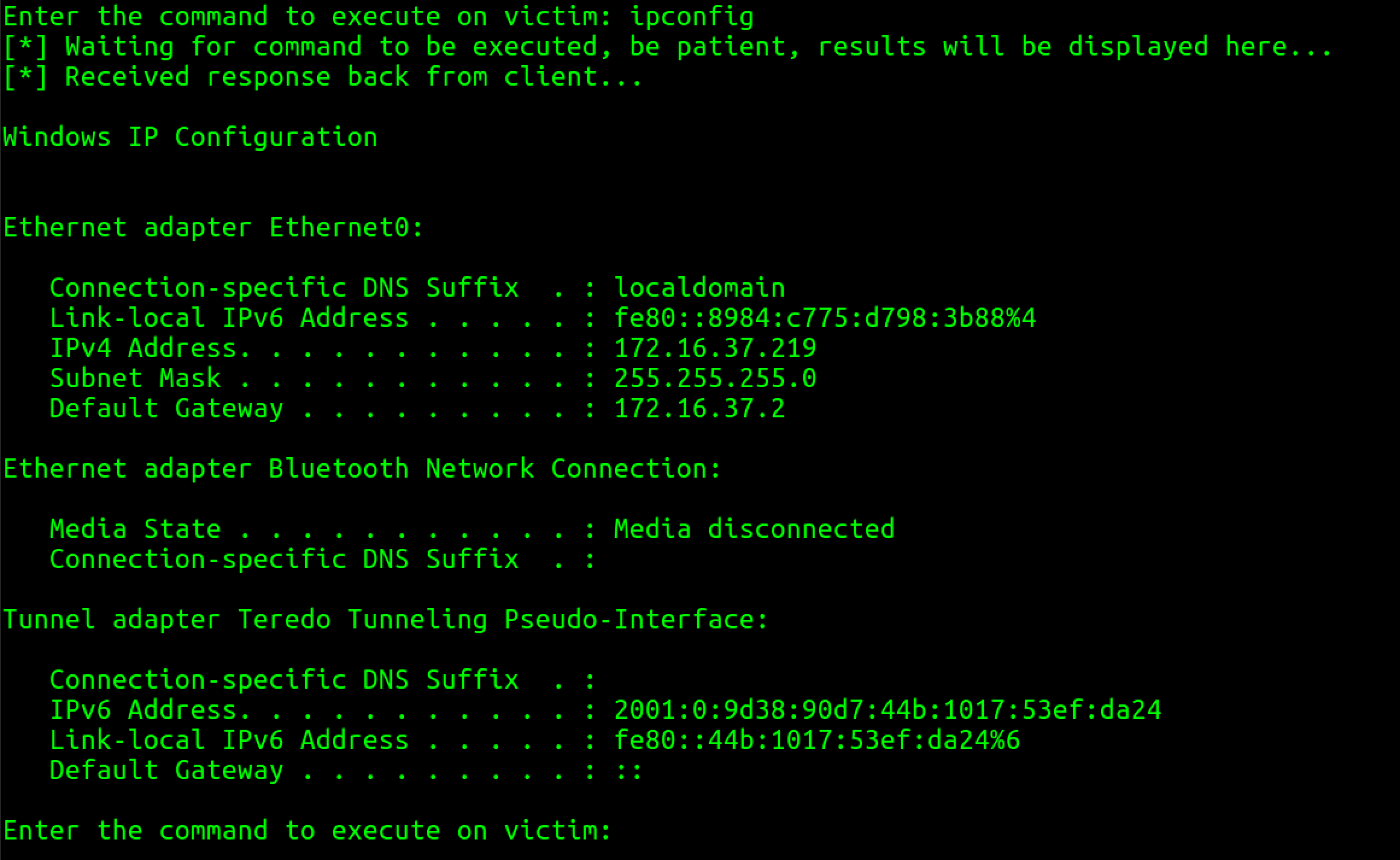
 Next we'll execute a command and wait for the random interval section (configurable) to communicate back with us and send us data:
Next we'll execute a command and wait for the random interval section (configurable) to communicate back with us and send us data:
 You can download TrevorC2 from our GitHub site: TrevorC2 Github DownloadTODO
You can download TrevorC2 from our GitHub site: TrevorC2 Github DownloadTODO
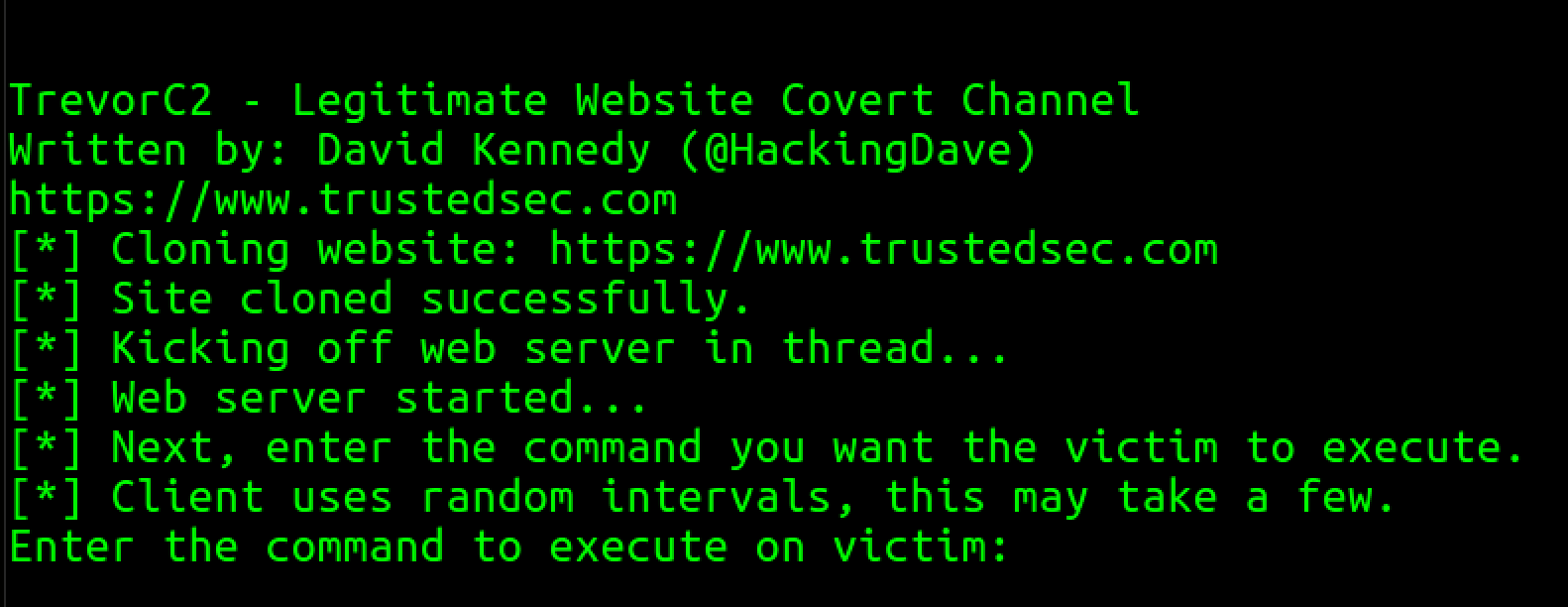
- trevor2_server.py - edit the file first, and customize, what website you want to clone, etc. The server will clone a website of your choosing and stand up a server. This server is browsable by anyone and looks like a legitimate website. Contained within the source is parameter that (again is configurable), which contains the instructions for the client. Once a client connects, it searches for that parameter, then uses it to execute commands.
- trevor2_client.py - all you need in any configurable option is the ability to call out to a website, parse some basic data, and then execute a command and then put the results in a base64 encoded query string parameter to the site. That's it, not hard.
Usage
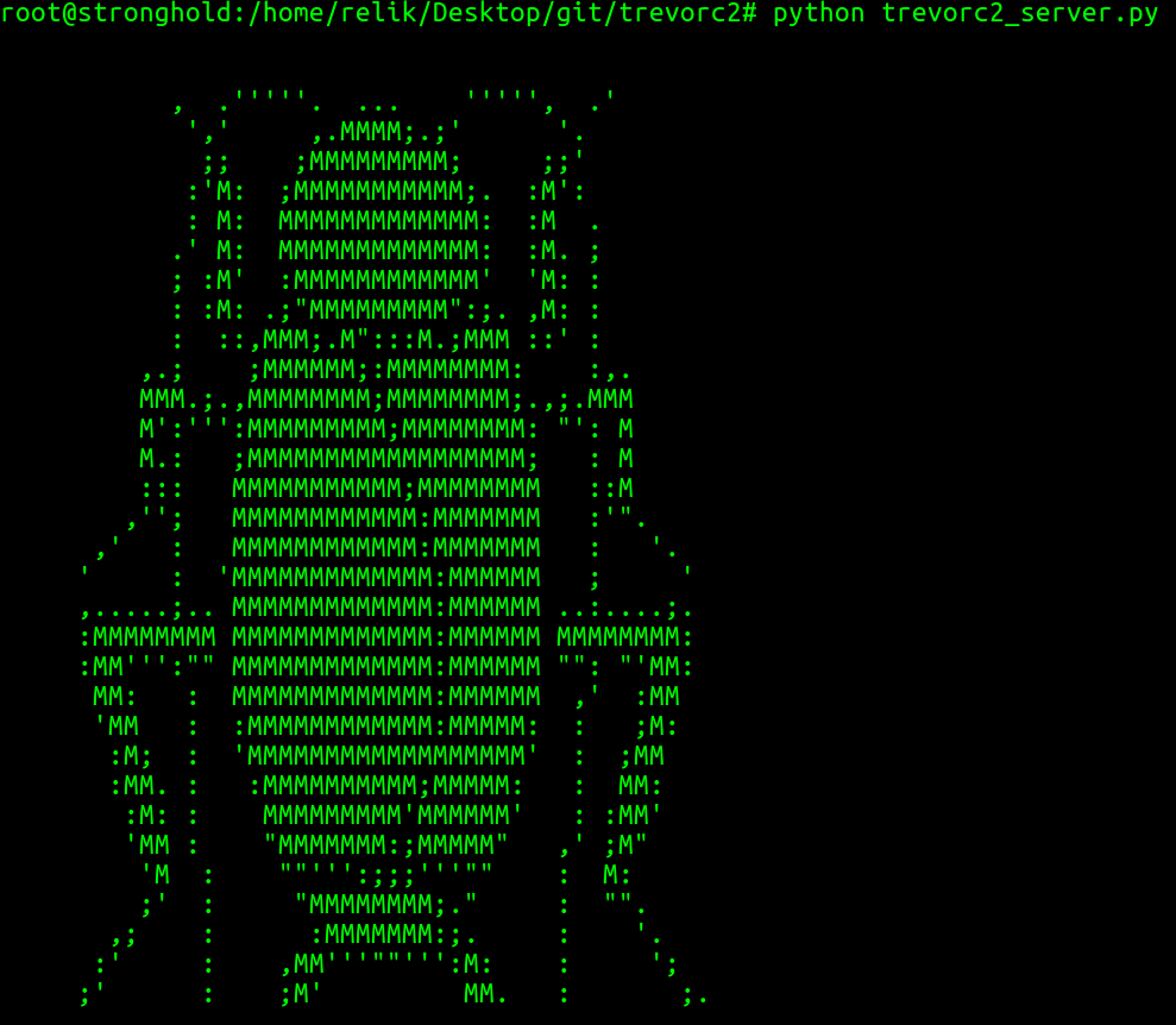
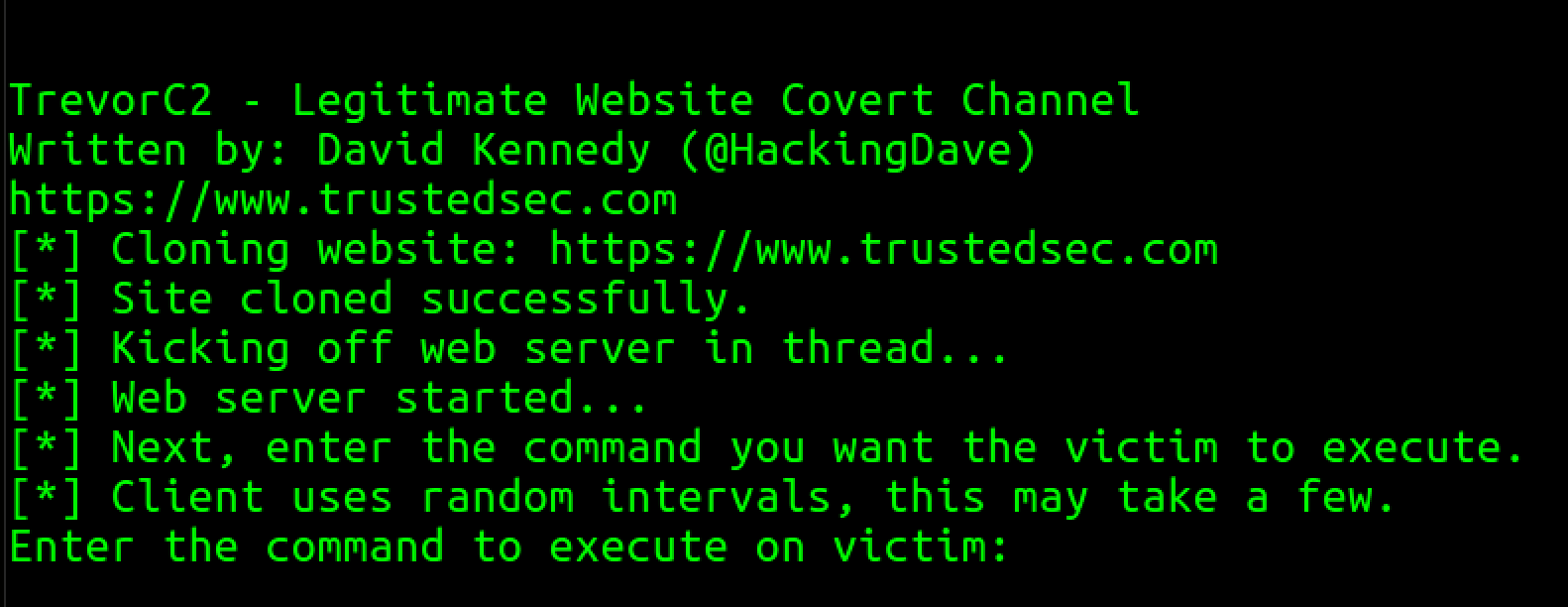
First edit the trevor2_server.py file and change the configuration options and site to clone.python trevor2_server.py
Next, edit the trevor2_client.py file and change the configuration and system you want it to communicate back to.
python trevor2_client.py
When running the trevor2_server, it will clone whatever website you specify when editing the file and modifying the url parameter.
In this example we'll clone https://www.trustedsec.com:
 Next we'll execute a command and wait for the random interval section (configurable) to communicate back with us and send us data:
Next we'll execute a command and wait for the random interval section (configurable) to communicate back with us and send us data:
 You can download TrevorC2 from our GitHub site: TrevorC2 Github DownloadTODO
You can download TrevorC2 from our GitHub site: TrevorC2 Github DownloadTODO- Add encryption (AES).
- Add randomized parameter names.
- Add a C# and PowerShell module.
- Add do_POST support for POST exfil on longer data.
- Add upload/download functionality.
- Add multi-threading for multiple shells