August 21, 2018
Tech Support Scams Are A Concern For All
Written by
Tyler Hudak
Incident Response
Incident Response & Forensics
Penetration Testing
Security Testing & Analysis

 Like many of you, I am the IT support for family and friends. As such, I get lots of calls concerning slow browsers, printers that won’t work, and questions that take me a few seconds to Google the answer to.
However, in the last few weeks, I’ve gotten a few calls with a similar story. Someone was having Internet issues and wanted to call their ISP. They didn’t know the number, so they searched for it in Google and called up the first number that popped up. This is all good, except when I hear the words “…and after they connected to my computer, they told me it was infected and could sell me a security plan,” I get very nervous. BIG. RED. FLAG. They had stumbled into a tech support scam.
[caption id="attachment_14767" align="aligncenter" width="974"]
Like many of you, I am the IT support for family and friends. As such, I get lots of calls concerning slow browsers, printers that won’t work, and questions that take me a few seconds to Google the answer to.
However, in the last few weeks, I’ve gotten a few calls with a similar story. Someone was having Internet issues and wanted to call their ISP. They didn’t know the number, so they searched for it in Google and called up the first number that popped up. This is all good, except when I hear the words “…and after they connected to my computer, they told me it was infected and could sell me a security plan,” I get very nervous. BIG. RED. FLAG. They had stumbled into a tech support scam.
[caption id="attachment_14767" align="aligncenter" width="974"]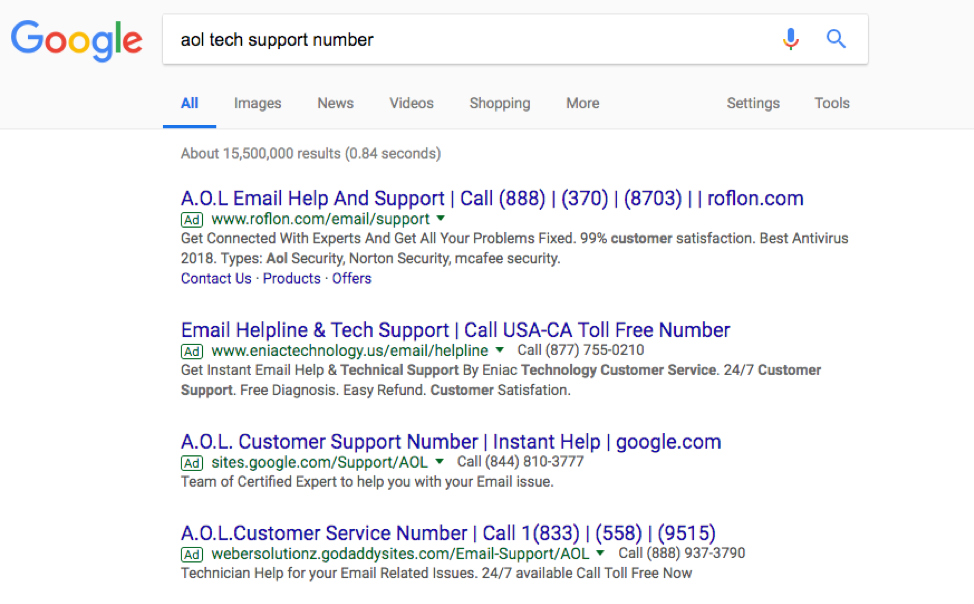 The first four ads when searching for “AOL tech support number” in Google are tech support scam pages.[/caption]
Victims are typically drawn into tech support scams through one of two ways. The first is the victim gets cold-called from “Microsoft” and told their computer is showing signs of compromise. The second occurs when a user clicks on the wrong link or ad, often when searching for something like “tech support,” as in the case above. The page they land on displays flashy pop-up windows, often with accompanying blaring sounds, stating multiple computer viruses have been detected and they need to call the number on the screen immediately.
[caption id="attachment_14768" align="aligncenter" width="974"]
The first four ads when searching for “AOL tech support number” in Google are tech support scam pages.[/caption]
Victims are typically drawn into tech support scams through one of two ways. The first is the victim gets cold-called from “Microsoft” and told their computer is showing signs of compromise. The second occurs when a user clicks on the wrong link or ad, often when searching for something like “tech support,” as in the case above. The page they land on displays flashy pop-up windows, often with accompanying blaring sounds, stating multiple computer viruses have been detected and they need to call the number on the screen immediately.
[caption id="attachment_14768" align="aligncenter" width="974"]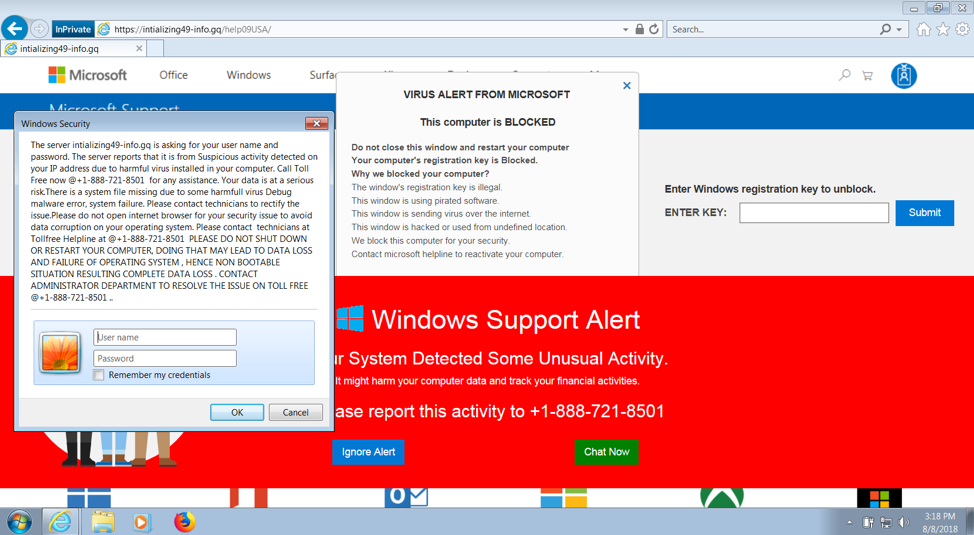 Sample tech support page[/caption]
Once on the phone, the scammer plies their scam. They convince the victim to download remote access software to allow the scammer access to the computer. Next, the scammer runs meaningless commands or downloads fake anti-virus software, stating the results mean the victim’s computer is infected with computer viruses. To fix this, the victim only has to pay a one-time fee to have them removed or can pay even more to be protected from here on out.
Obviously, this scam targets naive computer users and, on the surface, appears to be a home user problem. But should this be a concern for businesses too? Absolutely.
Let’s assume a user in your organization falls for this and examine the scam from its various steps.
Sample tech support page[/caption]
Once on the phone, the scammer plies their scam. They convince the victim to download remote access software to allow the scammer access to the computer. Next, the scammer runs meaningless commands or downloads fake anti-virus software, stating the results mean the victim’s computer is infected with computer viruses. To fix this, the victim only has to pay a one-time fee to have them removed or can pay even more to be protected from here on out.
Obviously, this scam targets naive computer users and, on the surface, appears to be a home user problem. But should this be a concern for businesses too? Absolutely.
Let’s assume a user in your organization falls for this and examine the scam from its various steps.
User clicks on malicious link.
Remote access software is downloaded, and an unauthorized third party connects to your system.
Commands are run, or programs are downloaded and executed.
- Treat the user as a victim. They got scammed and made a mistake. Do not threaten them with any type of corrective action, as that will only lead to other users becoming hesitant to report future compromises.
- Talk to the user and ask what the scammer did. This will help point your investigation down the right avenues.
- The scammer likely did not do anything to hide their activity, so forensic artifacts may be intact. Focus your analysis on browser history, file system timelines, event logs, and registry analysis to determine what occurred.
- Scam websites are often on unusual top-level domains (TLDs) such as .online, .support, .help, .top, or .xyz. Search for any activity with these or other odd domains and block them in your proxy server or firewall, or block them entirely on your DNS server. How much legitimate business do you do with .xyz domains?
- Use the incident as a stepping stone for user education. Informing your users of these scams will not only help them become more secure at home, it will raise their security awareness at work and keep your systems safe.
- If your policy allows it, report the tech support scam to the FTC at https://www.ftccomplaintassistant.gov/ as this will help get these scammers offline.