Intro to Web App Security Testing: Burp Suite Tips & Tricks

A brief list of useful things we wish we had known sooner
Burp Suite Pro can be complicated and intimidating. Even after learning and becoming comfortable with the core functionality, there remains a great deal of depth throughout Burp Suite, and many users may not stray far from the staples they know.
However, after years of testing with Burp Suite, members of the TrustedSec Software Security team have put together a brief list of useful features that have improved our testing, and things we wish we had known sooner. While these are not terribly complicated, they have had a positive impact on our workflow. Our hope is that by pointing some of these tips and tricks out, your testing will benefit as well.
Proxy
Burp Suite's proxy allows requests to be intercepted and modified between the browser and application. A useful trick, particularly when an application includes many additional, ancillary requests, is to intercept the response to a particular request.
Right-click > Do intercept > Response to this request
This helps cut through the noise when there is just one request/response pair you are interested in.
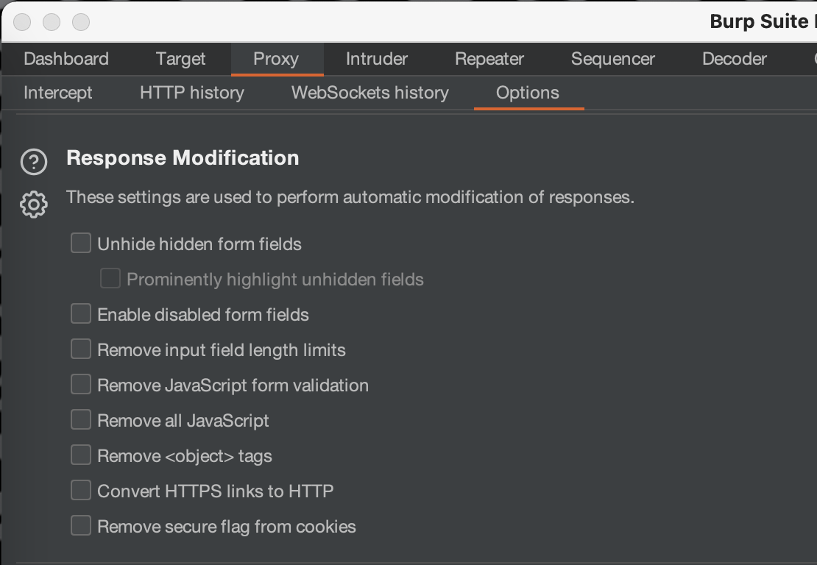
Applications often rely on client-side controls, like hidden fields or JavaScript validation, to enforce security controls. While these could be bypassed manually, that may slow testing down or simply become a pain. Another approach is to let Burp Suite remove them automatically with Response Modification options located under Proxy > Options > Response Modification.
Repeater
Burp Suite's Repeater functionality allows requests, each in their own tab, to be modified and resent over and over and serves as the basis for a lot of manual testing. After some time, however, many Repeater tabs with their own nondescript numerical title can get messy. Fortunately, double-clicking on the tab allows it to be renamed.
Tabs can also be dragged around within repeater to reorder them. This is particularly useful for processes involving multiple requests or for grouping similar requests together. Get your Repeater tabs in order before you try to demonstrate the issue to a client.
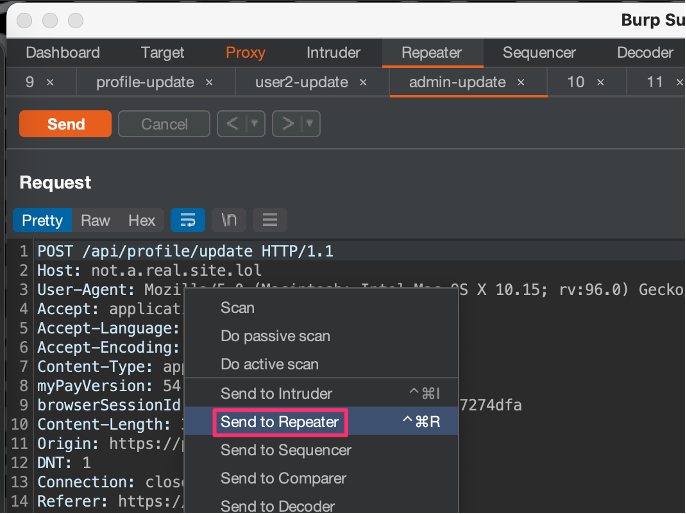
Another thing to note is that Repeater maintains a history of requests and their responses, but occasionally it is useful to start a new branch and take it in another direction or preserve a specific request/response. In these cases, you can send a Repeater request…to Repeater! Right-click > Send to Repeater
Intruder
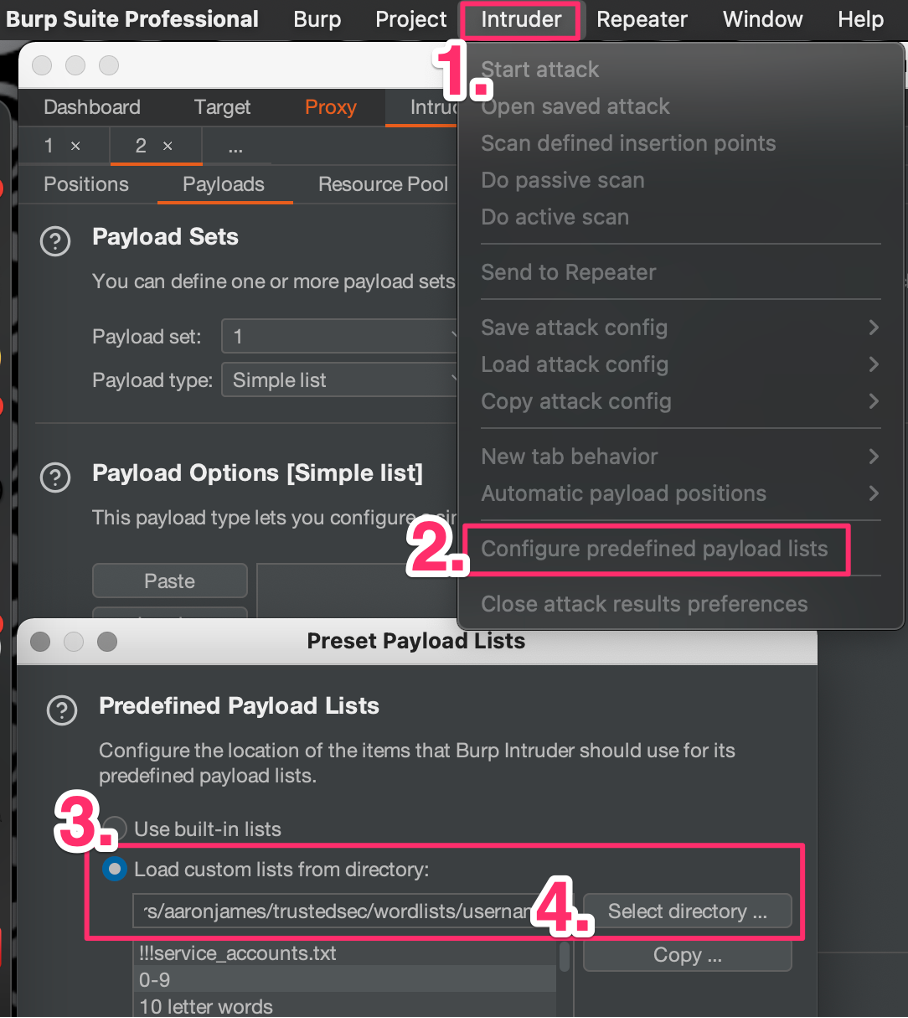
Burp Suite includes built-in wordlists that can be quickly added as payloads while configuring an attack, but if you need something specific, you'll have to load it from a directory. However, if there are a set of wordlists you use often and you don't want to have to browse for them, you can add these to the predefined payload list. Intruder > Configure predefined payload lists > Load custom lists from directory > Select directory …
Intruder attacks can occasionally run into issues due to network problems, rate limits, or an expired token of one form or another. However, rather than having to reconfigure and run another Intruder attack, it is possible to resend one or more requests from the Intruder results table. Select requests > Right-click > Request items again.
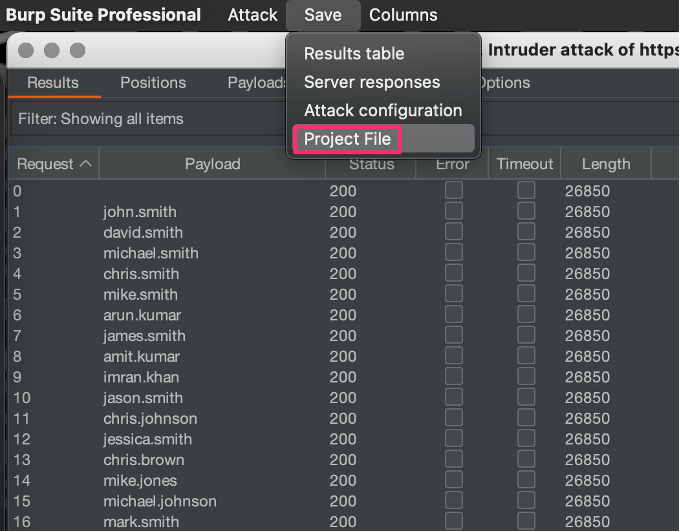
Have a results table from an Intruder attack you'd like to hang on to? Saving it to the project file will allow those results to persist across Burp Suite instances, unlike typical Intruder tabs. As far as I can tell, this only works for completed attacks, so you can't pause an attack, shut Burp Suite down, start it up again, and resume your attack. However, completed attacks won't be lost.
Scanning
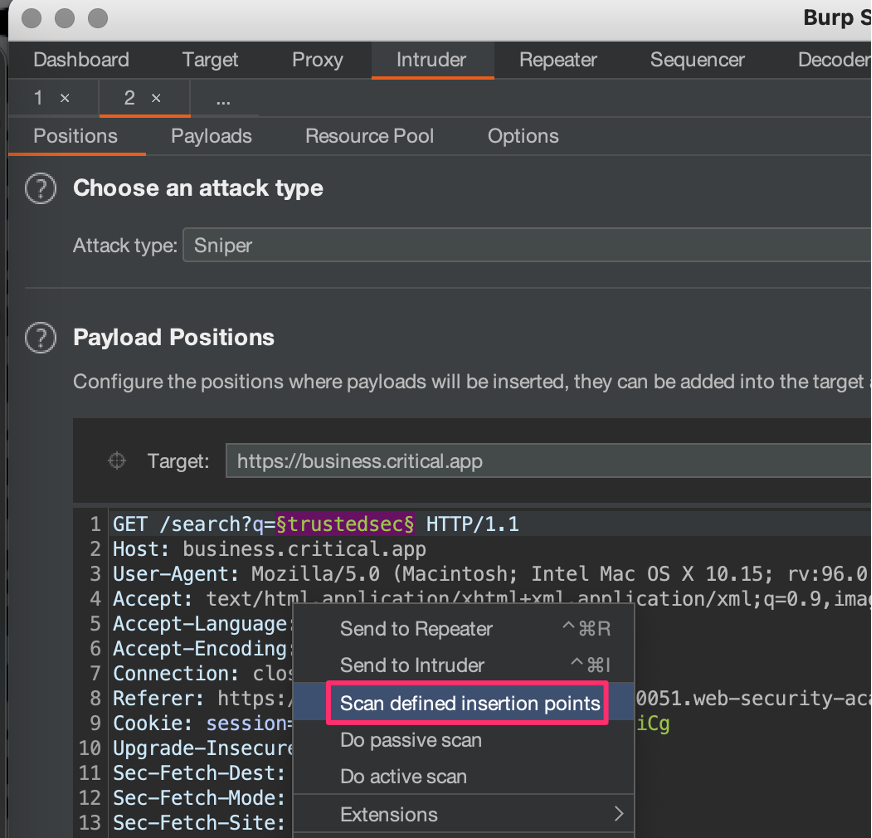
The handy way Intruder adds and clears insertion points for Intruder attacks is also an easy way to launch active scans against individual parameters you're interested in. From an Intruder pane, Right-click > Scan defined insertion points.
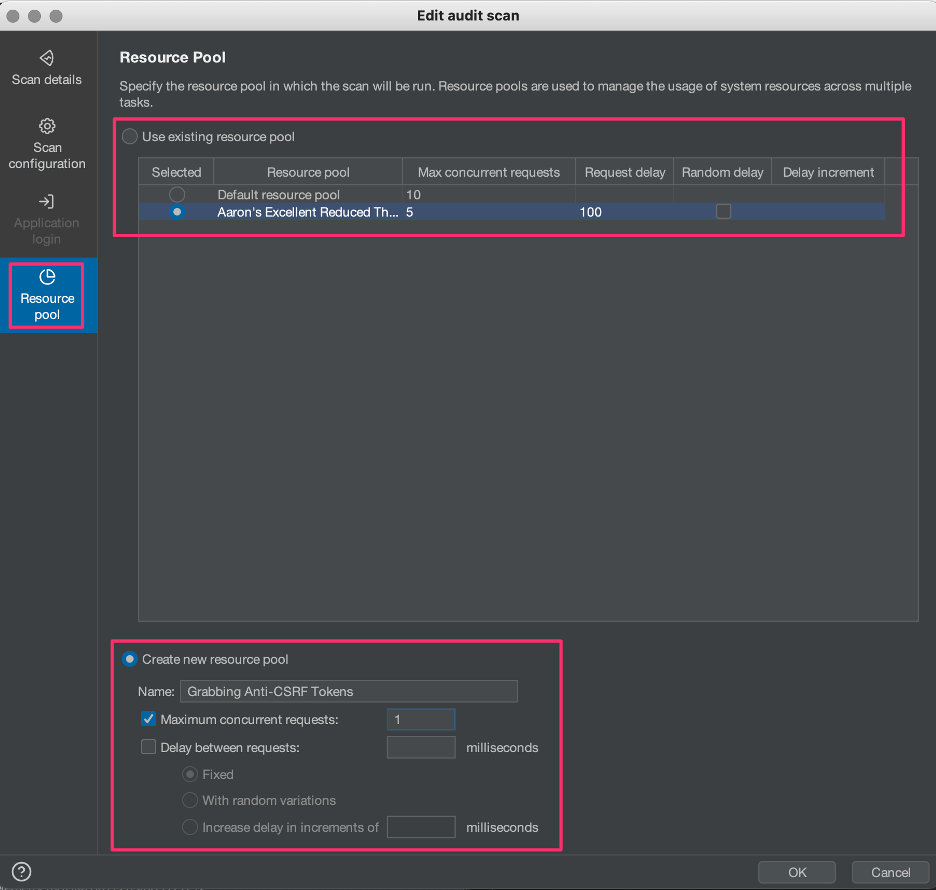
There are also many times when launching automated scans with Burp Suite's default settings is not the most appropriate, and you might consider creating one or more custom resource pools. While applying more threads to scans against robust applications can increase scanning speed, applications with poor stability or rate limiting may benefit from reduced scan threads or from a delay. Other situations, like when grabbing anti-CSRF tokens with macros, may require you to reduce scan threads to one (1).
General
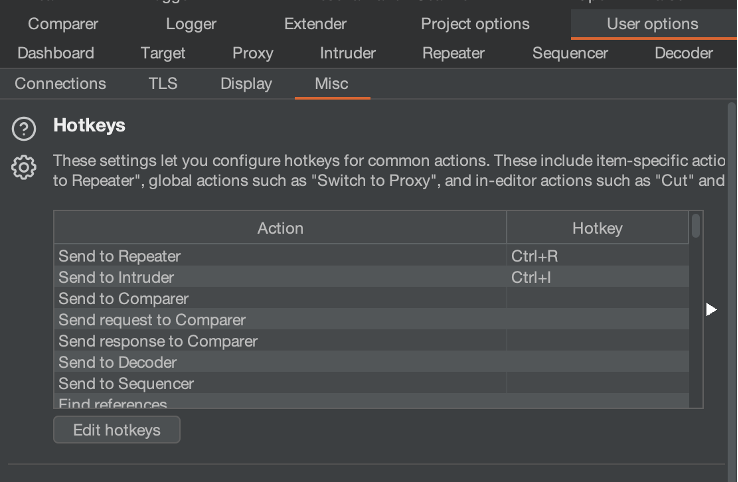
Burp Suite features hot keys to simplify and streamline routine functionality and UI navigation. For instance, under default settings, Ctrl+R can be used to send a request to Repeater or Ctrl+F to forward an intercepted proxy request. However, many more operations can be articulated through hot keys, and are customizable under User options > Misc > Hotkeys.
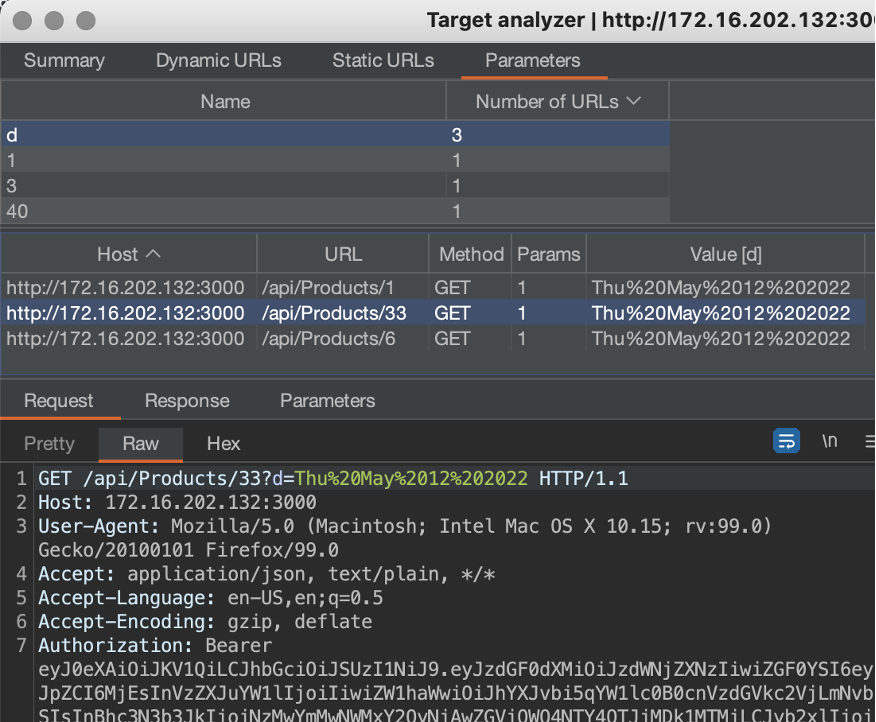
The target analyzer can be used to quickly identify application surface area as well as interesting dynamic URLs.
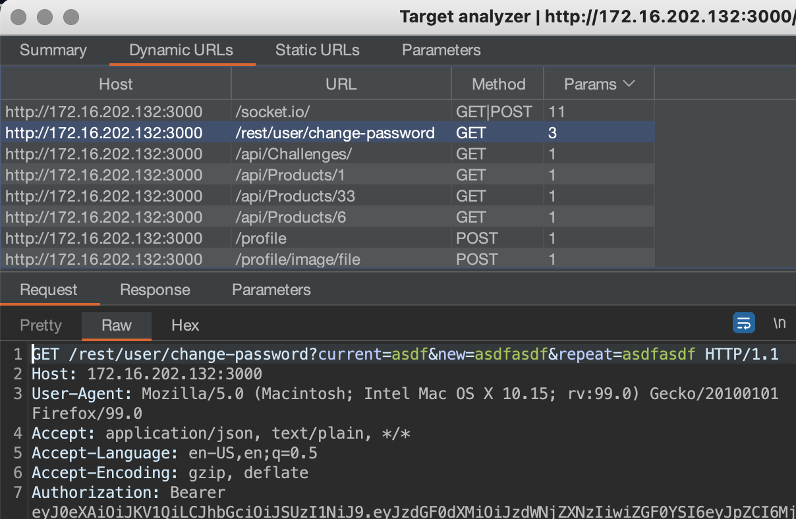
Run it by right-clicking a specific target in the site map selecting Engagement tools > Analyze target. The target analyzer can also be used to track down interesting parameters by demonstrating where they show up and what their values are.
Input for these tips came from the Software Security team at TrustedSec, and they all made the list because at some point, at least one of us did not know these tips were a thing. Some of these processes are a little unwieldy for me and I'm not sure I will adopt them, while others are so integral to my workflow that I forget anyone does it differently. Let us know which are useful to you, or if there are points of functionality we failed to mention that that you wish you had known about sooner.