November 17, 2017
Full Disclosure: Authenticated Command Execution Vulnerability in pfSense
Written by
Scott White

On 05/19/2016 Scott White of TrustedSec discovered an authenticated command injection vulnerability in pfSense. It was responsibly disclosed to pfSense ([email protected]) on 06/08/2016 and promptly fixed by the pfSense development team. TrustedSec wants to thank the pfSense team for the impressive response time and for providing a great open source project.
Although the vulnerability was discovered over a year ago and was publicly disclosed by pfSense (please see the security advisory at https://www.pfsense.org/security/advisories/pfSense-SA-16_08.webgui.asc), full exploitation details were not released. As some readers may or may not know, TrustedSec runs the DerbyCon CTF contest in Louisville, KY each year. When coming up with challenges for the contest each year, we try to incorporate real-world vulnerabilities alongside hacking methodologies and techniques that we regularly use as penetration testers. This year we decided to include a customized pfSense system requiring a multi-step hack in order to root the box.
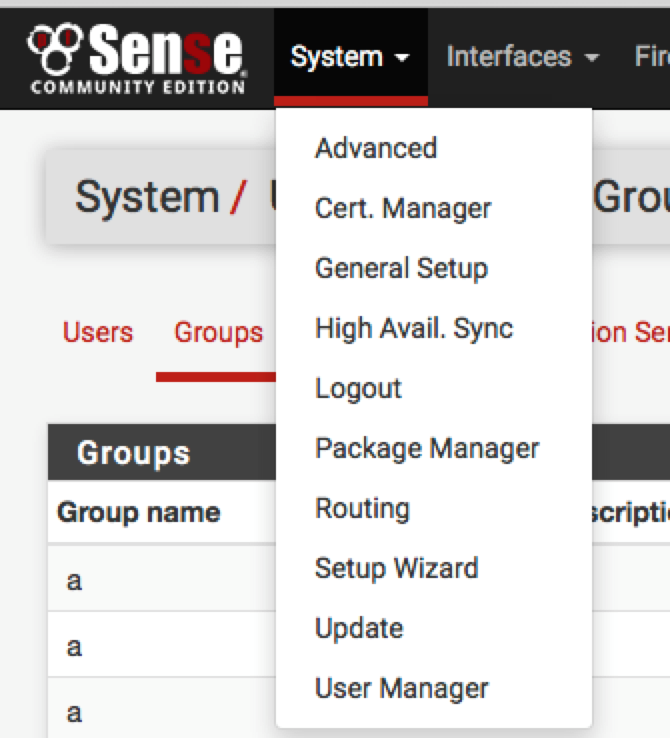
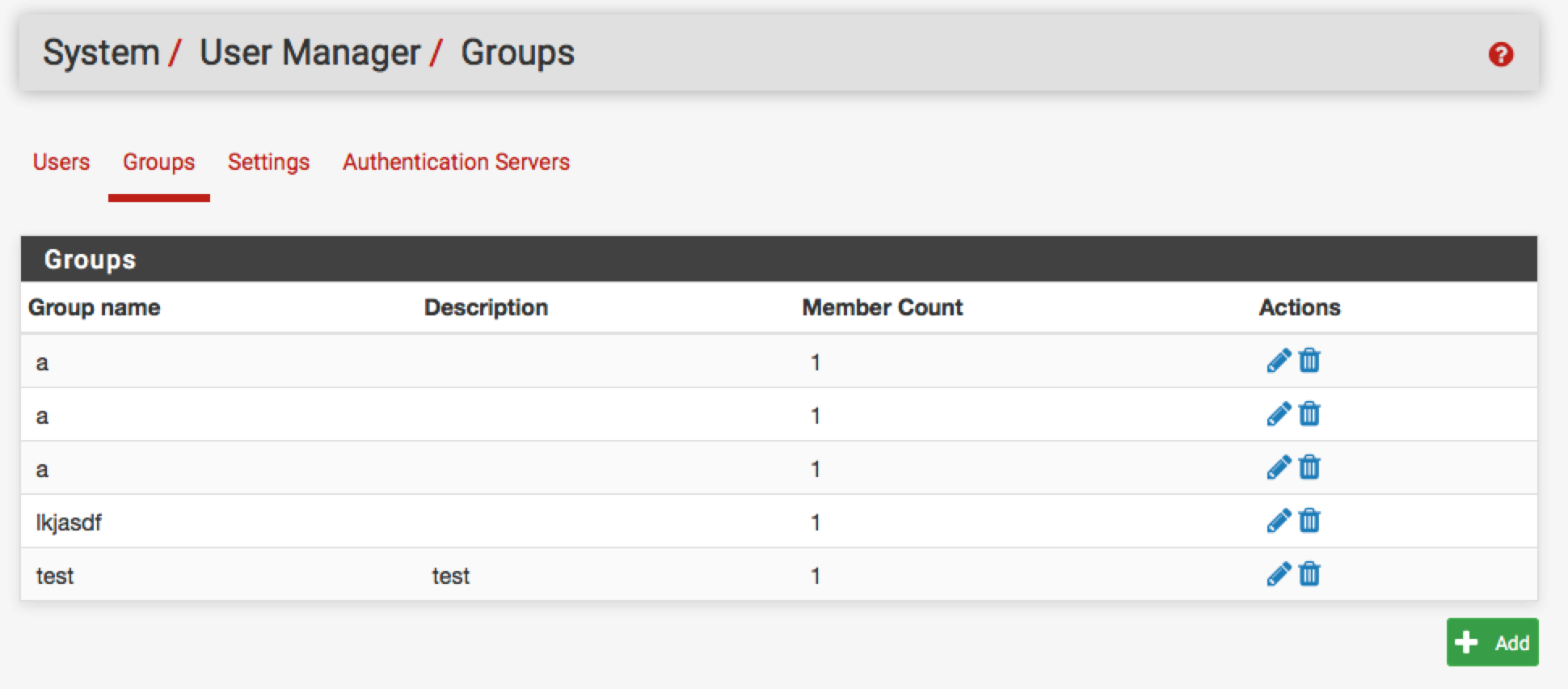
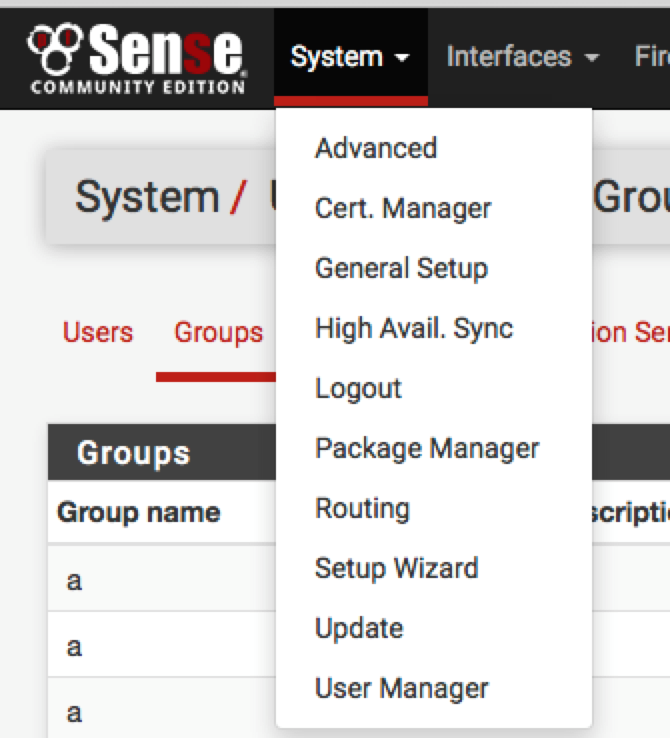
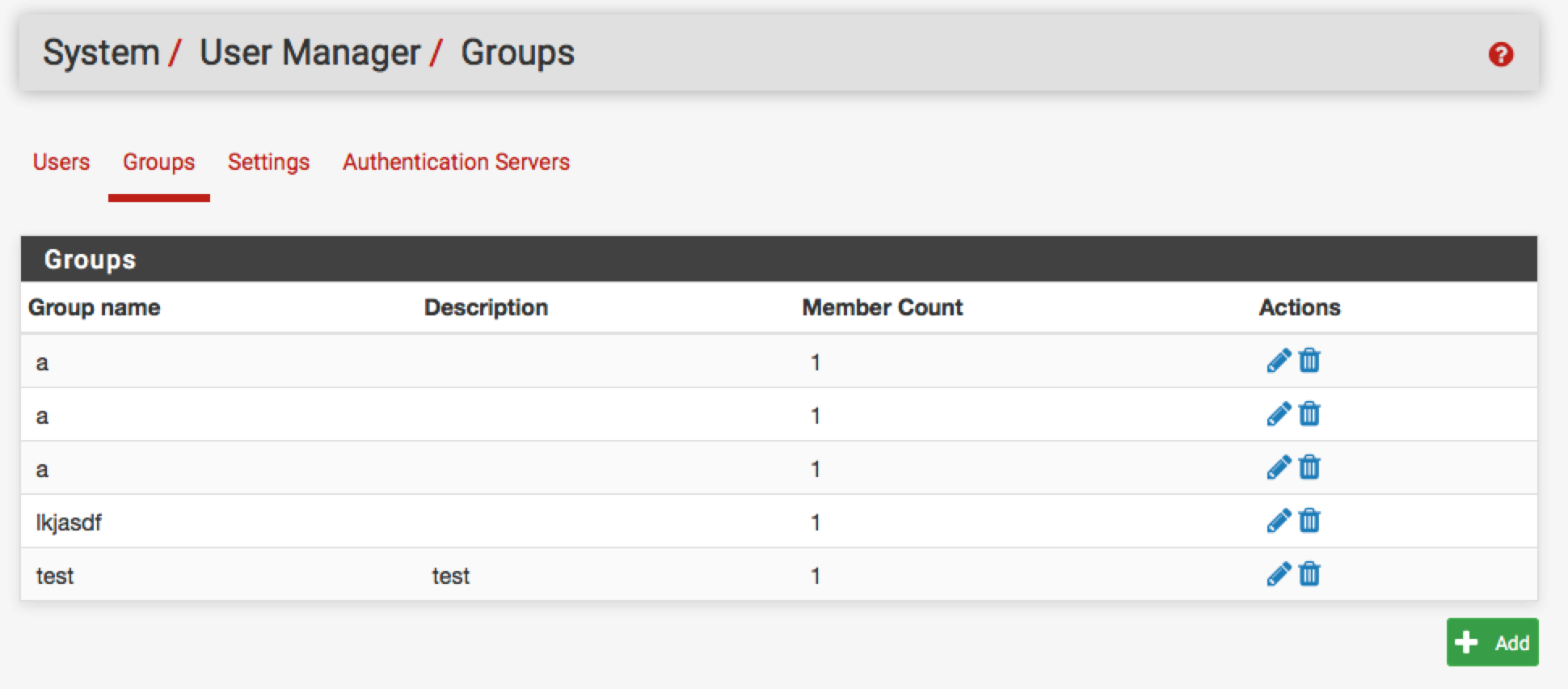
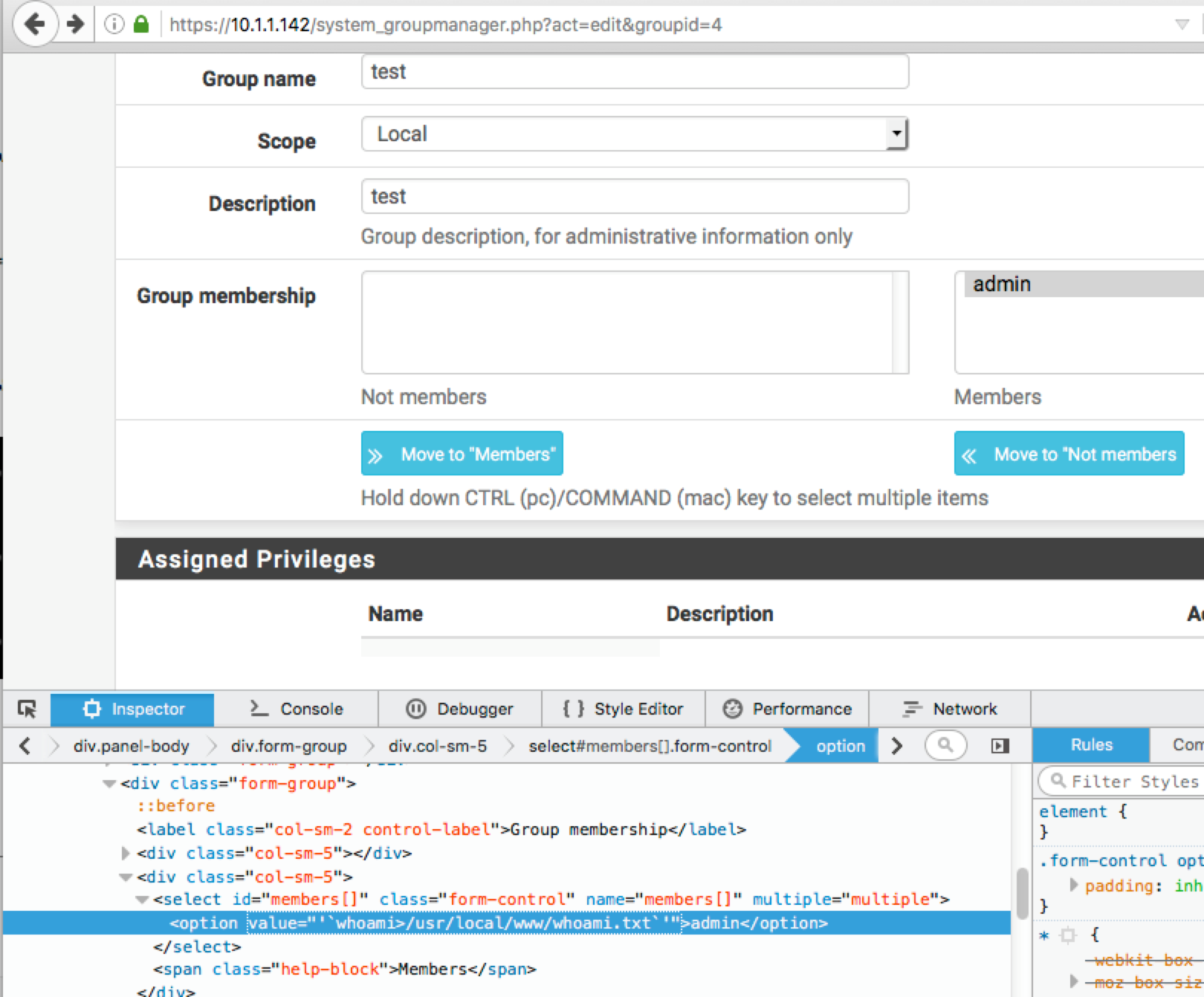
The command-injection vulnerability lies within auth.inc via system_groupmanager.php (System menu-->User Manager-->Groups) and is exploited using the “members” parameter.
 The vulnerability allows an authenticated WebGUI user with privileges for the system_groupmanager.php page to execute commands in the context of the root user.
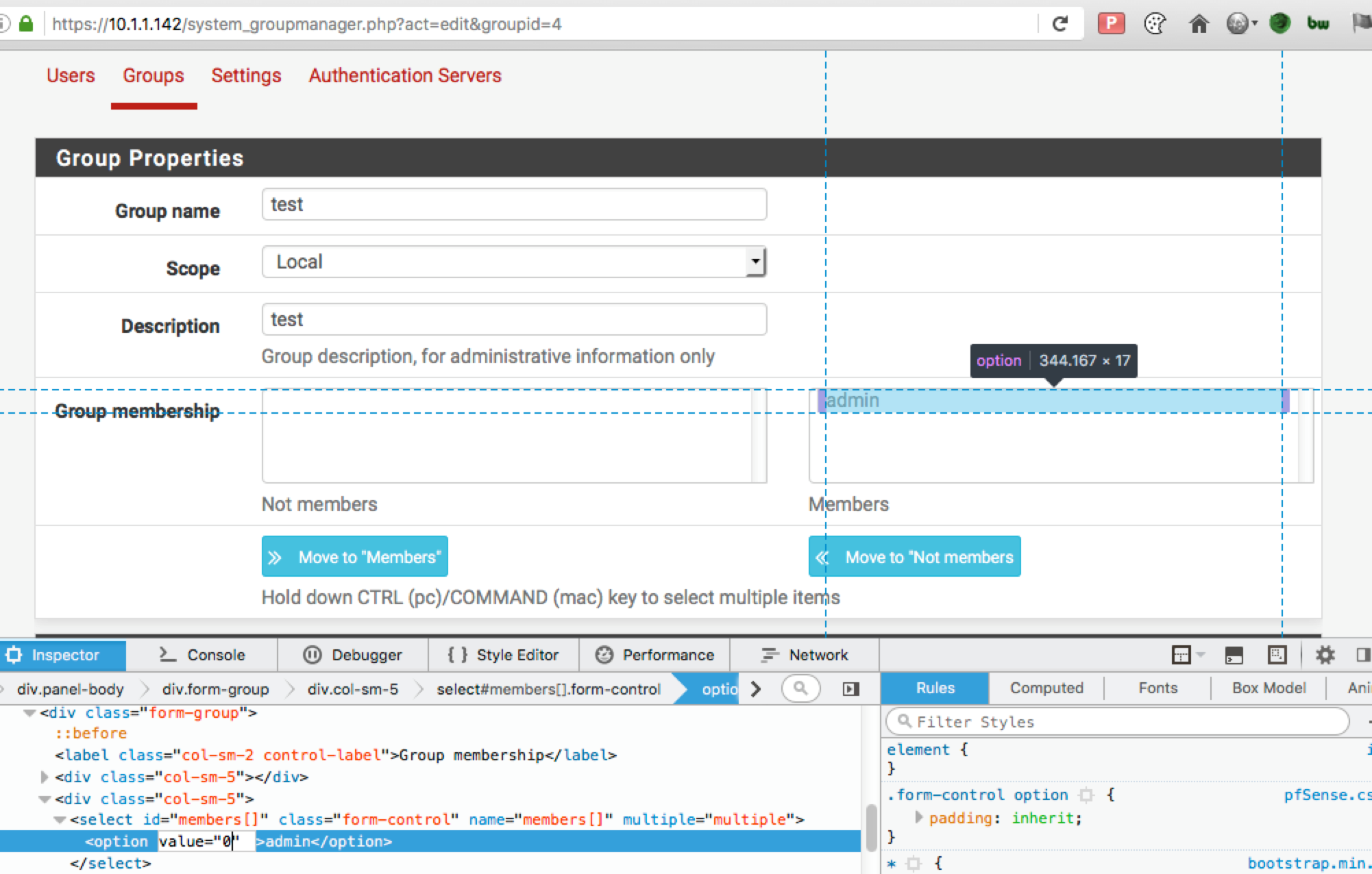
The following proof of concept example was used to demonstrate the presence of the vulnerability:
The vulnerability allows an authenticated WebGUI user with privileges for the system_groupmanager.php page to execute commands in the context of the root user.
The following proof of concept example was used to demonstrate the presence of the vulnerability:
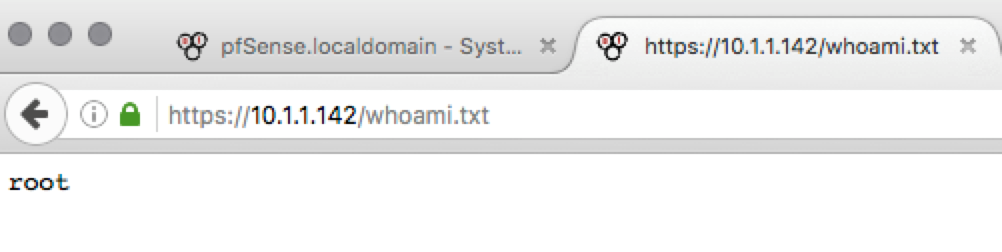
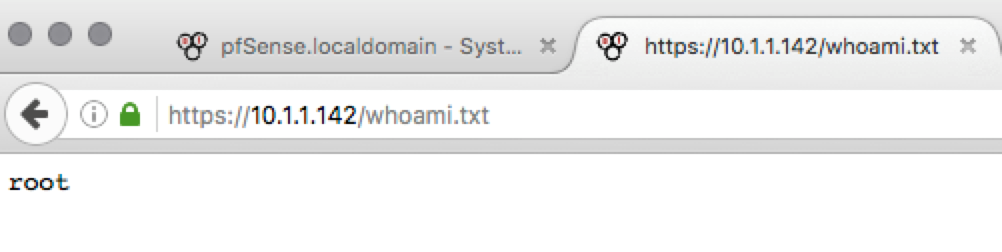
 The output of the command executed was then viewed in the webroot:
http://<address>/whoami.txt
The output of the command executed was then viewed in the webroot:
http://<address>/whoami.txt
 The winning team of the DerbyCon CTF, “SpicyWeasel”, has published their account of the contest (https://labs.nettitude.com/blog/derbycon-2017-ctf-write-up/) and solutions including how they managed to root the pfSense box. Since exploitation details are now public, we wanted to also illustrate the initial discovery payload which differed slightly from how the command execution was achieved during the CTF. The vulnerability details are also archived at https://www.exploit-db.com/exploits/43128/
The winning team of the DerbyCon CTF, “SpicyWeasel”, has published their account of the contest (https://labs.nettitude.com/blog/derbycon-2017-ctf-write-up/) and solutions including how they managed to root the pfSense box. Since exploitation details are now public, we wanted to also illustrate the initial discovery payload which differed slightly from how the command execution was achieved during the CTF. The vulnerability details are also archived at https://www.exploit-db.com/exploits/43128/
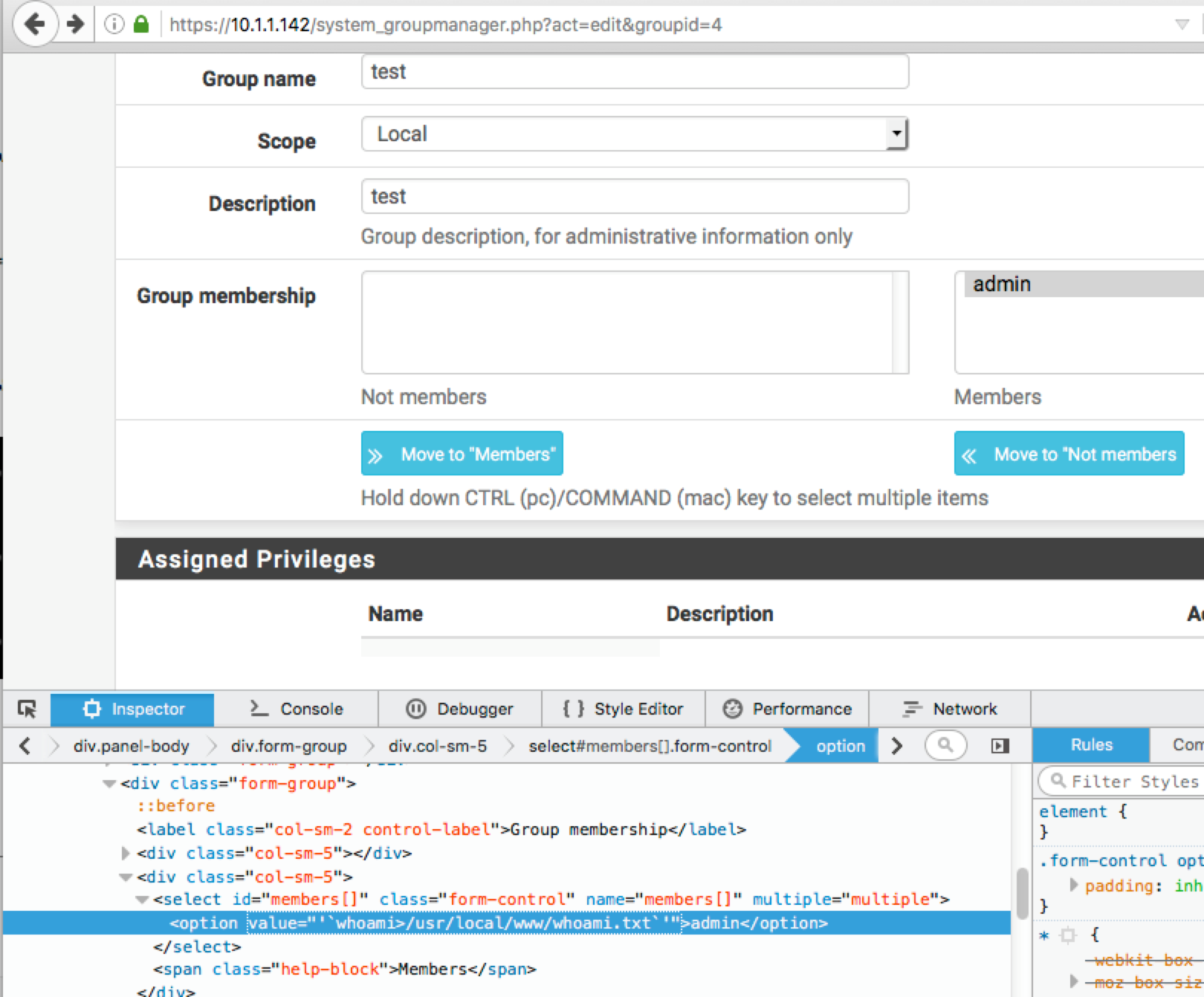
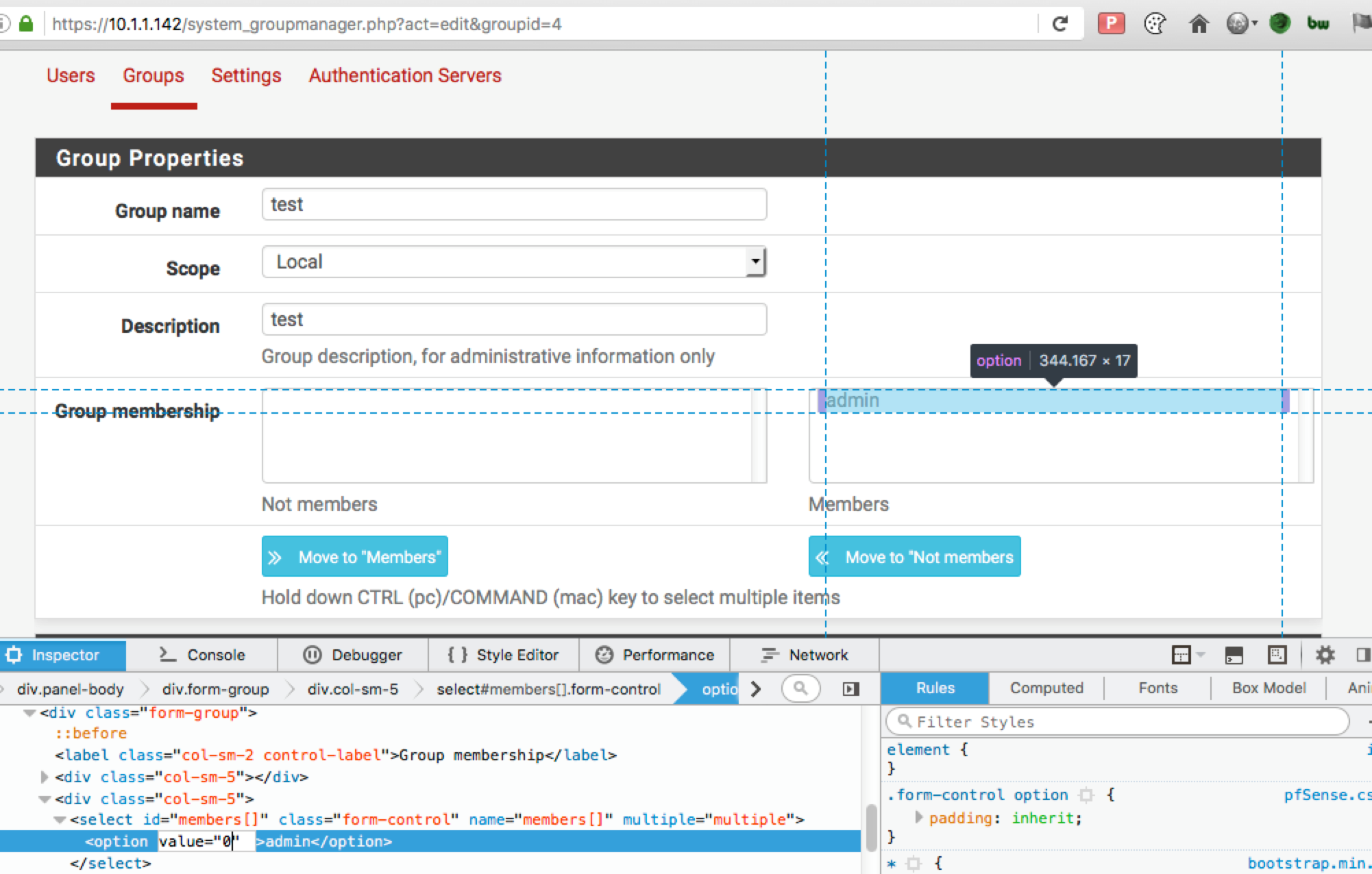 The vulnerability allows an authenticated WebGUI user with privileges for the system_groupmanager.php page to execute commands in the context of the root user.
The following proof of concept example was used to demonstrate the presence of the vulnerability:
The vulnerability allows an authenticated WebGUI user with privileges for the system_groupmanager.php page to execute commands in the context of the root user.
The following proof of concept example was used to demonstrate the presence of the vulnerability:
'`whoami>/usr/local/www/whoami.txt`'
 The output of the command executed was then viewed in the webroot:
http://<address>/whoami.txt
The output of the command executed was then viewed in the webroot:
http://<address>/whoami.txt
 The winning team of the DerbyCon CTF, “SpicyWeasel”, has published their account of the contest (https://labs.nettitude.com/blog/derbycon-2017-ctf-write-up/) and solutions including how they managed to root the pfSense box. Since exploitation details are now public, we wanted to also illustrate the initial discovery payload which differed slightly from how the command execution was achieved during the CTF. The vulnerability details are also archived at https://www.exploit-db.com/exploits/43128/
The winning team of the DerbyCon CTF, “SpicyWeasel”, has published their account of the contest (https://labs.nettitude.com/blog/derbycon-2017-ctf-write-up/) and solutions including how they managed to root the pfSense box. Since exploitation details are now public, we wanted to also illustrate the initial discovery payload which differed slightly from how the command execution was achieved during the CTF. The vulnerability details are also archived at https://www.exploit-db.com/exploits/43128/